(Apr 7) Updated openssl packages that fix one security issue are now available for Red Hat Enterprise Linux 6. The Red Hat Security Response Team has rated this update as having [More…]
As teased earlier, the first release candidate for WordPress 3.9 is now available for testing!
We hope to ship WordPress 3.9 next week, but we need your help to get there. If you haven’t tested 3.9 yet, there’s no time like the present. (Please, not on a production site, unless you’re adventurous.)
To test WordPress 3.9 RC1, try the WordPress Beta Tester plugin (you’ll want “bleeding edge nightlies”). Or you can download the release candidate here (zip). If you’d like to learn more about what’s new in WordPress 3.9, visit the work-in-progress About screen in your dashboard (![]() → About in the toolbar) and check out the Beta 1 post.
→ About in the toolbar) and check out the Beta 1 post.
Think you’ve found a bug? Please post to the Alpha/Beta area in the support forums. If any known issues come up, you’ll be able to find them here.
If you’re a plugin author, there are two important changes in particular to be aware of:
- TinyMCE received a major update, to version 4.0. Any editor plugins written for TinyMCE 3.x might require some updates. (If things broke, we’d like to hear about them so we can make adjustments.) For more, see TinyMCE’s migration guide and API documentation, and the notes on the core development blog.
- WordPress 3.9 now uses the MySQLi Improved extension for sites running PHP 5.5. Any plugins that made direct calls to
mysql_*functions will experience some problems on these sites. For more information, see the notes on the core development blog.
Be sure to follow along the core development blog, where we will be continuing to post notes for developers for 3.9. (For example, read this if you are using Masonry in your theme.) And please, please update your plugin’s Tested up to version in the readme to 3.9 before April 16.
Release candidate
This haiku’s the easy one
3.9 is near
WordPress 3.8.2 is now available. This is an important security release for all previous versions and we strongly encourage you to update your sites immediately.
This releases fixes a weakness that could let an attacker force their way into your site by forging authentication cookies. This was discovered and fixed by Jon Cave of the WordPress security team.
It also contains a fix to prevent a user with the Contributor role from improperly publishing posts. Reported by edik.
This release also fixes nine bugs and contains three other security hardening changes:
- Pass along additional information when processing pingbacks to help hosts identify potentially abusive requests.
- Fix a low-impact SQL injection by trusted users. Reported by Tom Adams of dxw.
- Prevent possible cross-domain scripting through Plupload, the third-party library WordPress uses for uploading files. Reported by Szymon Gruszecki.
We appreciated responsible disclosure of these security issues directly to our security team. For more information on all of the changes, see the release notes or consult the list of changes.
Download WordPress 3.8.2 or venture over to Dashboard → Updates and simply click “Update Now.”
Sites that support automatic background updates will be updated to WordPress 3.8.2 within 12 hours. If you are still on WordPress 3.7.1, you will be updated to 3.7.2, which contains the same security fixes as 3.8.2. We don’t support older versions, so please update to 3.8.2 for the latest and greatest.
Already testing WordPress 3.9? The first release candidate is now available (zip) and it contains these security fixes. Look for a full announcement later today; we expect to release 3.9 next week.
A serious overrun vulnerability in the
OpenSSL cryptographic library affects around 17% of SSL web servers which use certificates issued by trusted certificate authorities. Already commonly known as the
Heartbleed bug, a missing bounds check in the handling of the TLS heartbeat extension can allow remote attackers to view up to 64 kilobytes of memory on an affected server. This could allow attackers to retrieve private keys and ultimately decrypt the server’s encrypted traffic or even impersonate the server.
The Heartbleed bug write-up mentions
Apache and
nginx as being the most notable software using OpenSSL, and also points out that these have a combined active site market share of over 66% according to our
April 2014 Web Server Survey. However, not all of these servers are running an HTTPS service, nor are they all running vulnerable versions of OpenSSL with heartbeats enabled.
Our most recent
SSL Survey found that the heartbeat extension was enabled on 17.5% of SSL sites, accounting for around half a million certificates issued by trusted certificate authorities. These certificates are consequently vulnerable to being spoofed (through private key disclosure), allowing an attacker to impersonate the affected websites without raising any browser warnings.
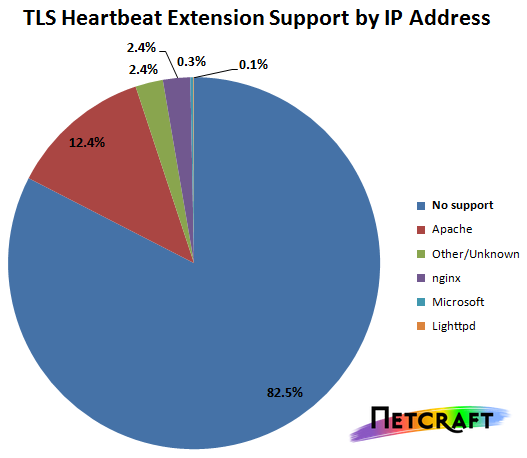
Note that a small percentage of Microsoft web servers also appear to support the TLS heartbeat extension; these are actually likely to be vulnerable Linux machines acting as reverse proxy frontends to Windows servers.
Support for heartbeats was added to OpenSSL 1.0.1 (released in 2012) by Robin Seggelmann, who also coauthored the
Transport Layer Security (TLS) and Datagram Transport Layer Security (DTLS) Heartbeat Extension RFC. The new code was committed to OpenSSL’s git repository just before midnight on new year’s eve 2011.
OpenSSL’s security advisory states that only versions 1.0.1 and 1.0.2-beta are affected, including 1.0.1f and 1.0.2-beta1. The vulnerability has been fixed in OpenSSL 1.0.1g, and users who are unable to upgrade immediately can disable heartbeat support by recompiling OpenSSL with the -DOPENSSL_NO_HEARTBEATS flag.
Popular sites which exhibit support for the TLS heartbeat extension include Twitter, GitHub, Yahoo, Tumblr, Steam, DropBox, HypoVereinsbank, PostFinance, Regents Bank, Commonwealth Bank of Australia, and the anonymous search engine DuckDuckGo.
Certificates and keys at risk of compromise should be revoked and replaced, particularly if they are used to protect sensitive data. Certificate Authorities, hosting companies and other interested parties can contact us for assistance in identifying affected certificates.
You can check whether your own HTTPS website might be vulnerable using the form below, and looking for the RFC6520 heartbeat TLS extension.
Netcraft site report
EasyApache 3.24.15 Released
SUMMARY
cPanel, Inc. has released EasyApache 3.24.15 with FCGI version 2.3.9 and PHP versions 5.5.10 and 5.4.27. This release addresses the FCGI vulnerability CVE-2013-4365 with fixes to a possible heap buffer overwrite issue, and the PHP vulnerability CVE-2013-7345 with fixes to bugs in the fileinfo module. We encourage all FCGI users to upgrade to FCGI version 2.3.9, and all PHP users to upgrade toPHP version 5.5.11 or PHP version 5.4.27.
AFFECTED VERSIONS
All versions of FCGI versions before 2.3.9.
SECURITY RATING
The National Vulnerability Database (NIST) has given the following severity ratings to these CVEs:
CVE-2013-4365 – MEDIUM
FCGI 2.3.9
Fixed a possible heap buffer overwrite issue related to CVE-2013-4365.
AFFECTED VERSIONS
All versions of PHP version 5.5 before 5.5.11.
All versions of PHP version 5.4 before 5.4.27.
SECURITY RATING
The National Vulnerability Database (NIST) has given the following severity ratings to these CVEs:
CVE-2013-7345 – MEDIUM
PHP 5.5.11
Fixed bug in the file info module related to CVE-2013-7345.
PHP 5.4.27
Fixed bug in the file info module related to CVE-2013-7345.
SOLUTION
cPanel, Inc. has released EasyApache 3.24.15 with FCGI version 3.2.9, and the updated versions of PHP 5.4 and 5.5 to correct these issues. Unless you have disabled EasyApache updates, EasyApache will include the latest versions of FCGI and PHP automatically. Run EasyApache to rebuild your profile with the latest version of FCGI and PHP.
REFERENCES
http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-4365
http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-7345
https://www.apache.org/dist/httpd/mod_fcgid/CHANGES-FCGID
http://www.php.net/ChangeLog-5.php#5.4.27
http://www.php.net/ChangeLog-5.php#5.5.11