An ongoing series of phishing attacks against the Steam gaming community is making effective use of look-alike domains to trick users into surrendering their usernames and passwords. The fraudsters behind these attacks then attempt to bypass Steam’s two-factor authentication with a malicious executable that is deceptively named SteamGuard.exe.

Victims are being targeted through Steam’s own chat client, giving fraudsters the opportunity to
spear phish accounts which are known to contain valuable tradable items. Since the inception of
Steam Trading, it has become easier to monetize stolen accounts by selling
the victim’s virtual items to other Steam users.
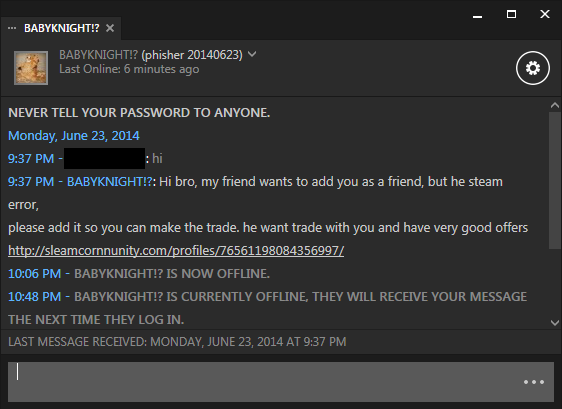
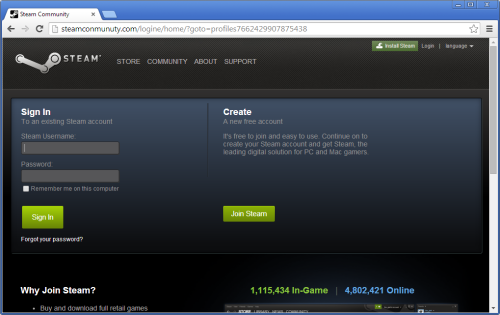
These sites use deceptive domain names, designed to look similar to the real steamcommunity.com.
If a targeted Steam user is persuaded to click on one of these links, he will be taken to a fake Steam profile. The following example shows another of these fake profiles on a similar look-alike domain. Profiles used in these attacks may appear to offer rare or unusual tradable items, and the high level and displayed XP score lends some degree of trustworthiness to potential trades.

To further entice the victim into trading with the fraudster, the fake profile also includes fabricated feedback which enhances the fraudster’s reputation as a fast and reliable trader.
However, the fraudster is not intending to trade any items with his victim — he instead wants to gain access to the victim’s account, and then steal the victim’s own tradable items. When the victim clicks on the “Add Friend” button, he will be presented with a spoofed login form on the look-alike domain that requests his Steam username and password:
The stolen username and password will not be of much use to the fraudster if the victim has enabled
Steam Guard. This two-factor authentication mechanism is enabled by default if the victim has a verified email address and has restarted Steam at least twice since verifying the address. If Steam Guard is enabled, the fraudster will be unable to access his victim’s Steam account without entering an access code which is emailed only to the victim.
Bypassing Steam’s two-factor authentication (Steam Guard)
Older Steam phishing sites simply asked the victim for their access code, but this approach is no longer suitable for trade fraudsters: there is now a time-delay before the trading feature can be used from a new device, which gives the victim an opportunity to recover his compromised account before any items can be traded by the fraudster.
Steam phishing sites consequently evolved to ask their victims to upload a special
ssfn file. This file is located in the victim’s Steam folder and acts as an authentication key, so that after providing a valid access code, the user does not have to keep on requesting and entering a new access code every time they launch Steam. If this file is copied to the fraudster’s computer, he will be able to bypass the two-factor authentication mechanism and gain access to the victim’s account.
The Steam phishing sites used in these latest attacks have evolved further still. Rather than tricking the victim into uploading the ssfn file, the phishing sites now display the following dialog box which prompts the victim to install a “special tool”:

Unsurprisingly, this special tool is actually malware designed to find and upload the victim’s ssfn file to the fraudster. The SteamGuard.exe file used in this particular attack is hosted on Google Drive, and submits the victim’s ssfn file to a hard-coded URL on the phishing site it was originally downloaded from.
After the fraudster has been furnished with the victim’s username, password and ssfn file, he will be able to login to the account and begin trading immediately.
Constant stream of look-alike domains
Since the start of May, more than a hundred look-alike domains have been registered specifically for the purpose of Steam phishing. More than a third of these phishing sites have been hosted in Russia, and many of the domains have also been registered to individuals with Russian addresses and email addresses at yandex.ru, a free webmail service.

Most of the domains used in these attacks have been registered under the .com top-level domain. One notable counterexample is steamcommunity.cm, which uses the country code top-level domain for
Cameroon. As well as being used in spear phishing attacks via Steam’s chat client, it is likely that this particular phishing site could also have also received
typo-traffic from Steam users.
More generally, the .cm ccTLD offers tremendous typosquatting opportunities against any corresponding .com domain. The domain’s operators received criticism
in the past when it wildcarded the entire .cm domain. It no longer does this, but there is evidently nothing stopping fraudsters from registering a .com domain’s corresponding .cm domain anyway.

Monetizing stolen Steam accounts
Albrecht Neumann, a mathematics student in Germany, is an active Steam trader who has reported some of these phishing attacks to Netcraft. He suspects the fraudsters are automatically searching trading portals for people who are offering to sell expensive items, and are then sending messages to those users via Steam: Each time he “bumps” a thread in which he is offering expensive items, he gets up to five new friend requests.
Neumann told Netcraft that keys and earbuds are a primary target for trade fraudsters, as these items serve as a relatively stable currency in the Steam economy, and are easy to turn into real money. Earbuds are cosmetic items which can be worn by a player’s in-game character, and were given away to Mac OS X users who played Team Fortress 2 during a limited time period in 2010; but now they can only be obtained through trading. Some users stockpile these items in the hope that their value might increase and earn them a profit further down the line. Such items are valuable by virtue of their rarity, and can often be sold for $30-$40 each, making some accounts worth thousands.
All of the domain names used in these attacks were very similar to the real steamcommunity.com domain. Netcraft’s
Fraud Detection service helps brand owners pre-emptively identify these types of fraudulent domain registrations. Some of the domains were registered months before the attacks actually took place, which would have allowed plenty of time to get them shut down before they were misused. Domain registrars are in a position to nip this in the bud even earlier — they can use Netcraft’s
Domain Registration Risk service to prevent their customers from registering domain names which are deceptively similar to well known phishing targets.




